Lets Encrypt is a free, automated and open Certificate Authority, an initiative supported by online big companies such as facebook, cisco etc to make web more safe.
I will be guiding you to setup Let’s Encrypt on Centos6.5/7 and nginx webserver. The following steps can be modified as according to your environment needs like other linux distros such as ubuntu etc. Setting this up on ubuntu shouldn’t differ much.
Here’s what you need to get started
- Centos 6.5/7 server where you have SSH access or shell access. (You must have SSH access to be able to use Let’s Encrypt)
- A registered domain name. www.yourdomainname.com
Steps:
- Point domain name to your server
You can point your domain name (both version along with www) to your server by configuring the proper A record provided by your web hosting, usually you do this by logging into your domain name account accessing DNS settings where you can enter the DNS settings, these process should be more or less same for various domain name providers. Let’s Encrypt will only issue certificate to a server which is accessible via domain name.
- Now access your Centos6.5/7 via SSH and install nginx webserver using following commands
Now start nginx
sudo systemctl start nginx
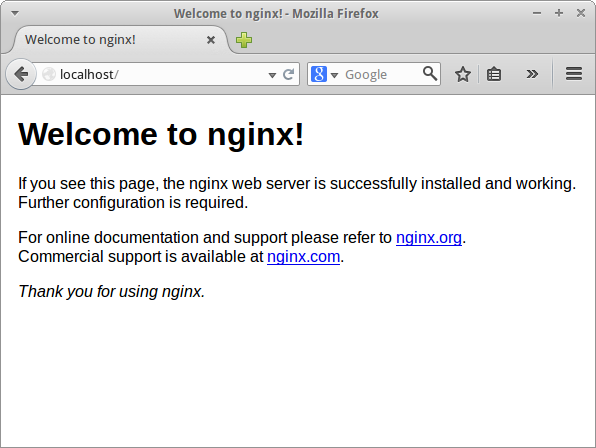
Now you should be able to go to http://www.yourdomainname.com and you should see something like this
sudo yum install epel-release sudo yum install nginx - Now Install Let’s Encrypt Client application using git
Clone and Install Let’s Encrypt from official github repository to your server at /opt/letsencrypt by
sudo git clonehttps://github.com/letsencrypt/letsencrypt/opt/letsencrypt
Install git sudo yum install git - Request SSL Certificate for yourdomainname.com
While running Let’s Encrypt SSL Certificate request script it listens on port 80 for Let’s Encrypt to verify that the domain name belongs to your server, so we need to close any programs that is currently running on port 80. So we need to shutdown our nginx server for now, if your are running on different version of Centos the commands to restart, stop, start nginx could be different.
Usually following command should work
Now to stop nginx
sudo systemctl stop nginx
Now Request SSL Certificate
Use the standalone plugin to request for certificate by executing following command
At the first prompt add your email address and second prompt domain names as follows
[email protected] and yourdomainname.com www.yourdomainname.com
If everything goes well the script will output a message with your certificate expiry date usually in 3 months.
cd /opt/letsencrypt./letsencrypt-auto certonly –standalone - Now configure nginx to use the Let’s Encrypt Certificate by
Now change the server block and comment out 2 lines with listen 80 and add listen 443 ssl; for eg:
Now add your domain names and ssl certificate like this
Now add a server block to redirect port 80 traffic to port 443
Now Save and exit the file and start nginx to put the changes into effect by
sudo systemctl start nginx
At this point your SSL certificate should be in place and you can test by visiting your domain name.
sudo nano /etc/nginx/sites-available/default# listen 80 default_server; # listen [::]:80 default_server ipv6only=on; listen 443 ssl;server_name yourdomainname.com www.yourdomainname.com; ssl on; ssl_certificate /etc/letsencrypt/live/yourdomainname.com/fullchain.pem; ssl_certificate_key /etc/letsencrypt/live/yourdomainname.com/privkey.pem; root /usr/share/nginx/html; index index.html index.htm; ssl_protocols TLSv1 TLSv1.1 TLSv1.2; ssl_prefer_server_ciphers on; ssl_ciphers 'EECDH+AESGCM:EDH+AES256+EECDH:AES256+EDH';server { listen 80; server_name yourdomainname.com www.yourdomainname.com; location / { return 301 https://www.yourdomainname.com$request_uri; } } - Since Let’s Encrypt Certificate are valid for 90 days you can automate that renewal process.
Here’s how you do it
Add the following location block under ssl server block on your nginx configuration
Next we need to setup Let’s Encrypt configuration file for automation of SSL Certificate request. Copy cli.ini to /usr/local/etc/le-renew-webroot.ini
Now edit the configuration file to fit your needs
Uncomment line with email and add your email which you entered before such as
Uncomment line with domains and add domains as follows (maintaining the order)
Then uncomment the webroot path and make sure it matches the webroot path specified in you nginx configuration as follows
Now cd into cd /opt/letsencrypt and test the renewal request script using the following command
Assuming the configuration are correct the script should output Congratulation message with expiry date of the certificate. If the expiry date is less than 30 days the renewal request will be sent.
Now to automate the autorenewal process we will be using a shell script and use a cronjob that will schedule this script to be run every week.
Now download the script by using following command
sudo curl -L -o /usr/local/sbin/le-renew-webroothttp://do.co/le-nginx-renewMake it executable
The le-renew-webroot script takes an argument the domain name whose certificate you want to check for renewal. If the renewal isn’t necessary it will simply output the remaining days to expire with the domain name.
Now run a cronjob to execute this script to check for certificate renewal every week by running following command
sudo nano -c /etc/crontab
Then add this line to execute the script every monday at 1:30 am, the output of the log will be saved on /var/log/le-renewal.log
Save and exit the cron file.location ~ /.well-known { allow all; }sudo cp /opt/letsencrypt/examples/cli.ini /usr/local/etc/le-renew-webroot.inisudo nano /usr/local/etc/le-renew-webroot.iniemail = [email protected]domains = yourdomainname.com, www.yourdomainname.comwebroot-path = /usr/share/nginx/htmlcd /opt/letsencrypt ./letsencrypt-auto certonly -a webroot --renew-by-default --config /usr/local/etc/le-renew-webroot.inisudo chmod +x /usr/local/sbin/le-renew-webroot30 1 * * 1 /usr/local/sbin/le-renew-webroot >> /var/log/le-renewal.log
Now your domain is using a Free SSL/TLS Certificate from Let’s Encrypt with auto renewal every 3 months.